No organization can fight cybercrime alone. The most resilient companies share what they know — and learn from what others have seen. Here’s why that matters more than ever.
Let’s be honest — keeping up with cyber threats can feel like an exhausting game of whack-a-mole. New attack vectors pop up daily, threat actors constantly shift their tactics, and the sheer volume of vulnerabilities can overwhelm even the most well-staffed security teams. But here’s the thing: you don’t have to face this alone. Threat intelligence sharing is one of the most powerful, practical strategies organizations can adopt to level the playing field.
Why Does Sharing Actually Matter?
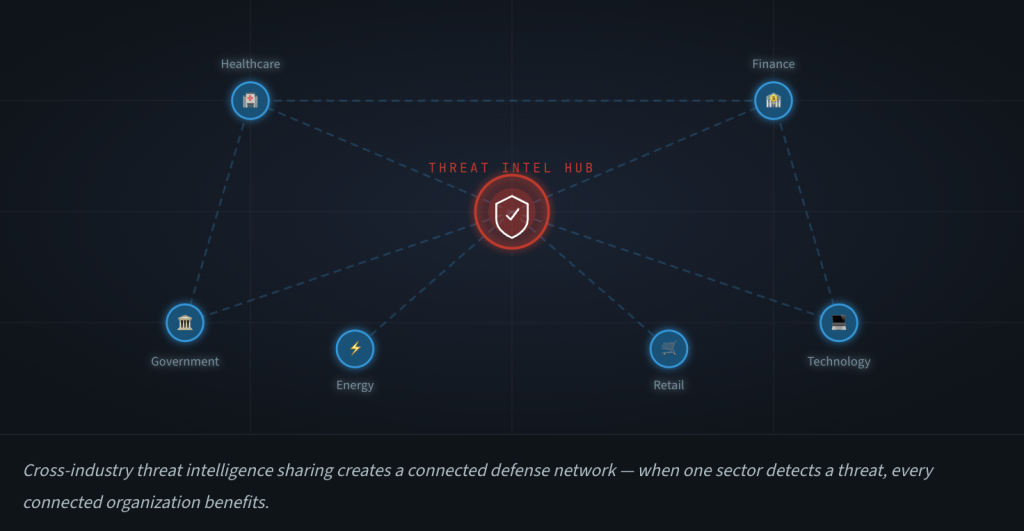
Think of it this way. If a hospital in Chicago gets hit by a novel ransomware variant on Monday morning, that intelligence — the indicators of compromise, the tactics used, the entry point exploited — could help a bank in London patch a similar vulnerability before the attackers ever reach their door. That’s the promise of threat intelligence sharing: turning one organization’s bad day into a warning that protects hundreds of others.
Cyber threats don’t respect industry boundaries, and they certainly don’t care about geography. Attackers routinely reuse tools, techniques, and infrastructure across targets. When defenders share what they’ve seen, they’re essentially building a collective early-warning system. It’s not just nice to have — in a landscape where adversaries openly collaborate on dark web forums and share their own tools, it’s arguably essential.
Better Detection, Faster Response
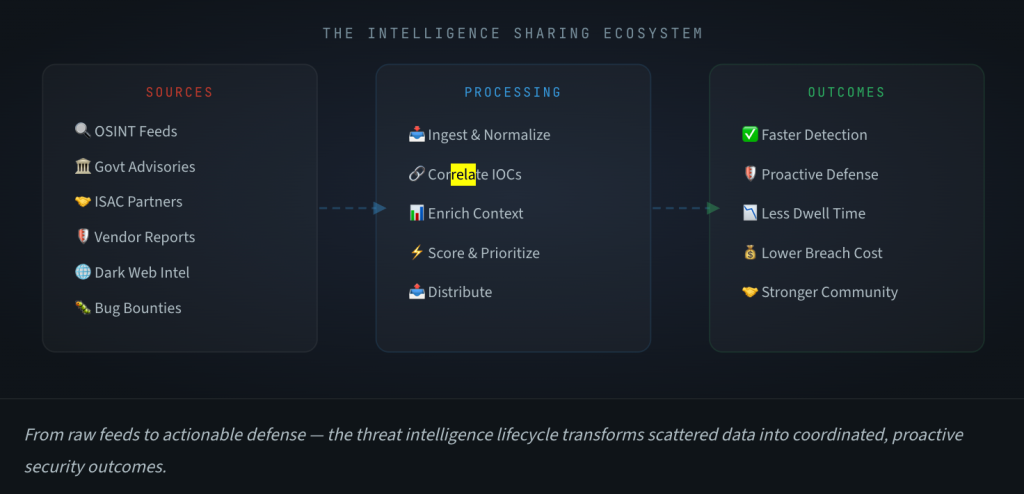
One of the most immediate benefits of sharing threat intelligence is how dramatically it improves an organization’s ability to spot trouble early. Instead of relying solely on what your own sensors and logs reveal, you gain access to a collective pool of insights — from industry peers, government agencies, ISACs, and cybersecurity vendors — that broadens your visibility into the threat landscape.
This is especially valuable for catching threats that are specifically designed to evade standard defenses. A sophisticated phishing campaign targeting financial services, for instance, might slip past your email filters. But if another organization in your sector has already identified the campaign and shared the relevant indicators, your team can proactively hunt for those same signatures before any damage is done.
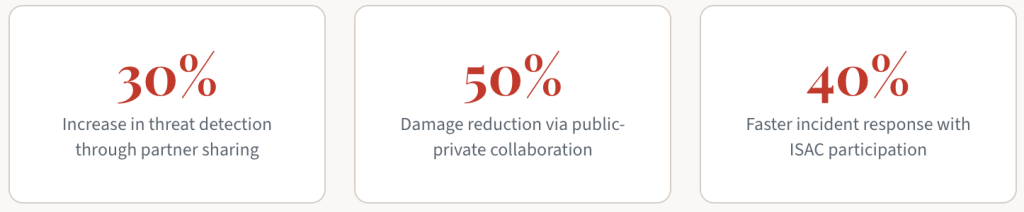
Organizations that participate in active threat intelligence sharing programs report up to 40% faster incident response times and significantly reduced dwell time for undetected threats.
Speed matters. The faster you can detect, triage, and respond to an incident, the less damage it causes. Shared intelligence compresses that timeline by giving defenders a head start — you’re not starting from scratch when an attack begins, because you’ve already seen the playbook.
Preventing Tomorrow’s Attacks Today
Here’s where threat intelligence sharing gets really interesting. It’s not just about reacting to what’s already happened — it’s about getting ahead of what’s coming next. When organizations pool their knowledge about the tactics, techniques, and procedures (TTPs) being used by threat actors, patterns start to emerge. Those patterns become predictive.
Say your industry peers report a series of attacks exploiting a particular supply chain vulnerability. Even if you haven’t been targeted yet, that intelligence lets you audit your own supply chain, patch the relevant systems, and harden your defenses preemptively. You’re not waiting for the knock at the door — you’ve already reinforced it.
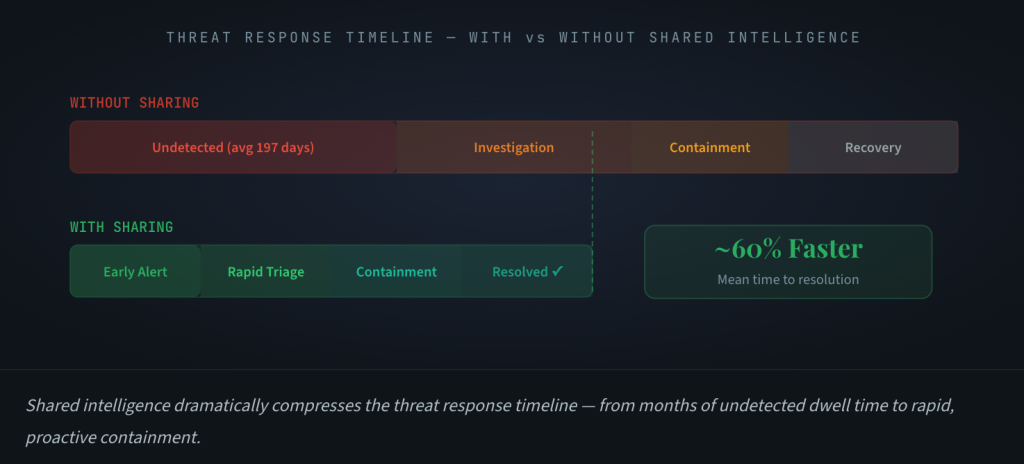
This shift from reactive to proactive security is arguably the single most valuable outcome of threat intelligence sharing. It transforms cybersecurity from a perpetual firefighting exercise into something more strategic and forward-looking.
◆
The Honest Challenges
Of course, if threat intelligence sharing were easy, everyone would be doing it perfectly already. The reality is that real barriers exist, and it’s worth understanding them honestly so we can work past them.
Legal and Privacy Hesitations
Many organizations worry — understandably — about the legal implications of sharing sensitive threat data. What if sharing an indicator inadvertently exposes customer information? What if it violates a regulatory framework or a contractual obligation? These aren’t hypothetical concerns. The lack of universal, clear-cut legal frameworks for threat intelligence sharing means that legal teams often default to caution, and caution usually means keeping things internal.
The good news is that initiatives like the Cybersecurity Information Sharing Act (CISA) in the United States and similar frameworks internationally are slowly creating safer legal ground for organizations to share intelligence without exposing themselves to liability. But there’s still work to be done, especially for smaller organizations that may lack the legal resources to navigate these complexities.
Technical Standardization
Even when organizations want to share, the technical side can be frustrating. Different platforms use different formats, different taxonomies, different APIs. Feeding threat data from one system into another often requires custom integrations that take time and money to build and maintain. Standards like STIX/TAXII have helped enormously, but adoption is still uneven across industries and regions.
Making It Work: Practical Advice
If you’re ready to take threat intelligence sharing seriously — and you should be — here’s what actually matters in practice.
First, start with clear internal guidelines. Define what types of intelligence you’ll share, with whom, through what channels, and under what conditions. This removes ambiguity and gives your team confidence to act. Second, prioritize quality over volume. A handful of well-contextualized, actionable indicators is worth far more than a firehose of raw IOCs with no context. And third, invest in relationships. The most effective intelligence sharing happens within trusted communities — ISACs, sector-specific groups, or even informal networks of peer CISOs. Trust is the currency that makes this work.
Real-World Results
The evidence is compelling. When two companies partnered to share threat intelligence across their networks, they saw a 30% improvement in threat detection and mitigation. When government agencies worked alongside private sector organizations during a sophisticated cyber-attack, the collaborative response cut potential damages in half. And across entire sectors, ISAC-facilitated information exchange has reduced average incident response times by 40%.
Cross-industry sharing has proven equally valuable. Financial services organizations sharing intelligence with healthcare providers, for example, have enabled early identification and mitigation of ransomware campaigns targeting hospitals — campaigns that might have gone undetected without that cross-sector visibility. These aren’t theoretical benefits; they’re measured outcomes from organizations that committed to collaboration.
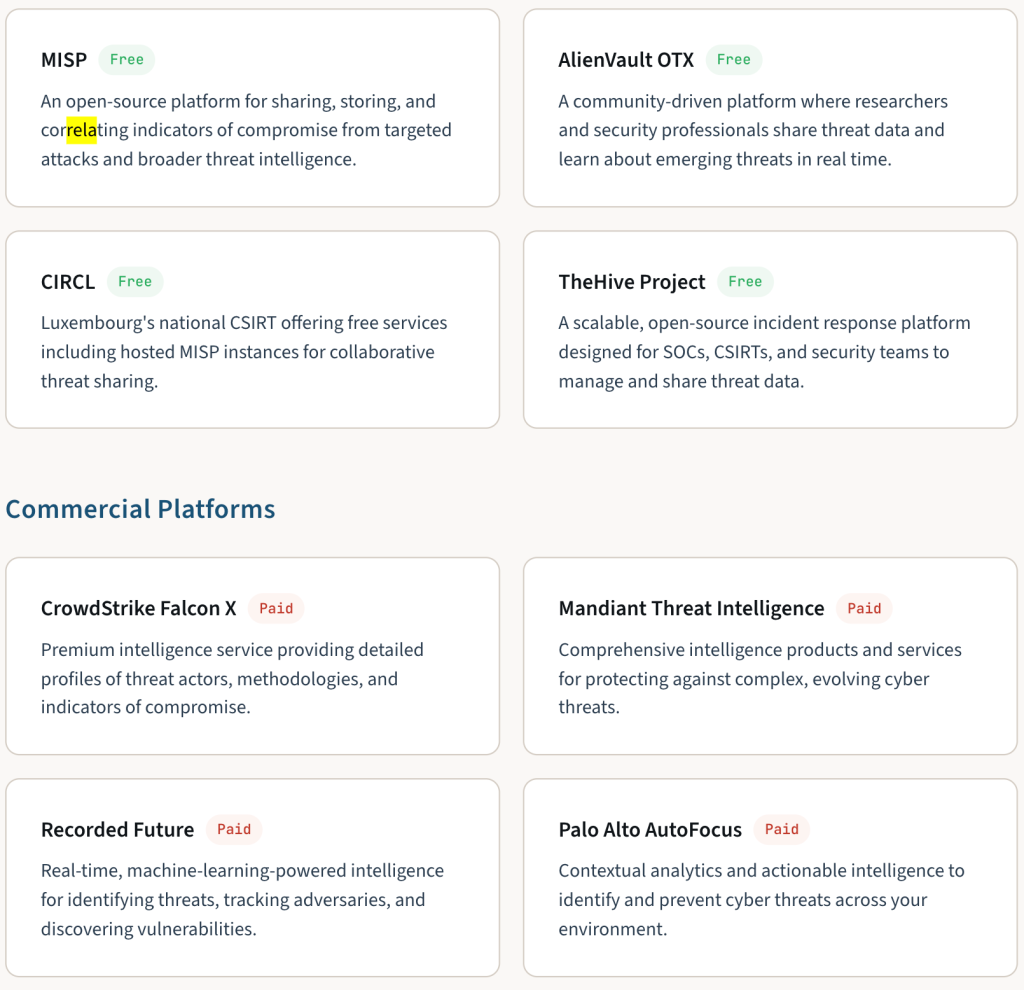
Notable Threat Intelligence Platforms
Whether you’re just starting out or looking to upgrade your capabilities, these platforms facilitate the kind of intelligence exchange that strengthens collective defense.
Open Source Platforms
Key Takeaways
- Early detection saves everything. Shared intelligence gives your team a head start on threats you haven’t encountered yet, turning other organizations’ experiences into your proactive defense.
- Collaboration multiplies your resources. No single organization can monitor the entire threat landscape. Pooling intelligence with trusted partners is a cost-effective force multiplier.
- Diverse perspectives sharpen analysis. Cross-industry sharing surfaces patterns and connections that a single-sector view would miss entirely.
- Faster response, less damage. Organizations in active sharing programs consistently demonstrate shorter dwell times and reduced incident impact.
- Compliance becomes easier. Many regulatory frameworks now expect or require intelligence sharing as part of a mature cybersecurity program.
◆
Frequently Asked Questions
Why is threat intelligence sharing crucial for a strong cybersecurity strategy?
No organization can fully understand the threat landscape on its own. Sharing intelligence creates a collective defense that helps everyone stay updated on the latest threats, vulnerabilities, and attacker behavior — making it far harder for adversaries to reuse the same playbook across multiple targets.
How does sharing actually improve my defenses?
Shared intelligence gives your security team advance warning of threats they haven’t yet encountered. This means you can update detection rules, patch vulnerable systems, and adjust your security posture before an attack reaches your network — rather than scrambling to respond after the fact.
What are the real benefits of participating in sharing initiatives?
You gain access to a much broader pool of threat data, improve your incident response speed, and build relationships with other security professionals who can be invaluable during a crisis. The practical result is a more resilient security program at lower overall cost.
How can we keep shared intelligence confidential and secure?
Use encrypted communication channels, establish clear data-sharing agreements with trusted partners, implement access controls around sensitive indicators, and leverage platforms designed specifically for secure intelligence exchange (like MISP or commercial TIP solutions). Regular access reviews and TLP (Traffic Light Protocol) markings help maintain confidentiality.
Does sharing really help prevent attacks, or just improve response?
Both. While faster incident response is an immediate benefit, the real power is in prevention. When you learn about adversary TTPs being used against peers in your sector, you can proactively harden your environment against those specific techniques — stopping attacks before they ever begin.
Final Thoughts
The cybersecurity community’s greatest advantage over adversaries isn’t any single tool or technology — it’s the ability to work together. Threat intelligence sharing transforms isolated security operations into a connected, adaptive defense ecosystem where every participant gets stronger.
If your organization isn’t already participating in structured intelligence sharing — through an ISAC, an industry consortium, or even informal peer networks — now is the time to start. The threats are only getting more sophisticated, and the organizations that thrive will be the ones that recognized early that cybersecurity is a team sport.