What this is about: Managed Extended Detection and Response (M-XDR/MDR) is the capability to continuously monitor your environment, spot suspicious behavior early, and respond fast—before a “small alert” becomes a real incident. The big decision is whether you build and run this capability yourself, or you pay a provider (an MSSP) to run it for you.
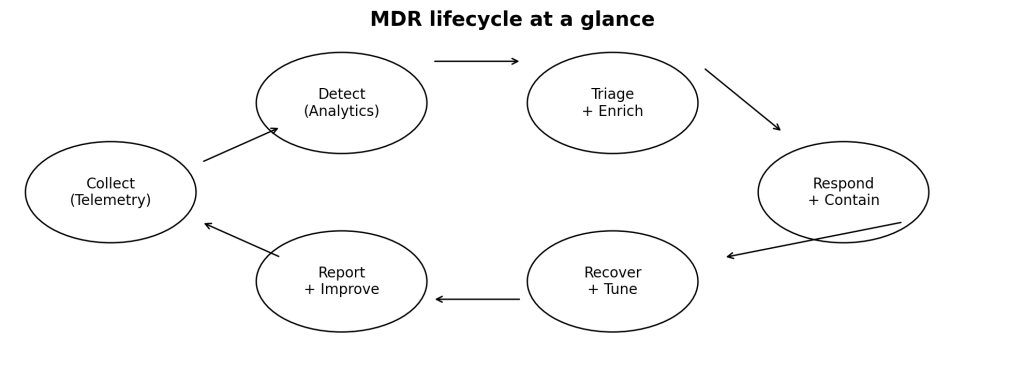
What an MDR / M-XDR program typically includes
- 24×7 monitoring of security telemetry across endpoints, identity, network, cloud, and email.
- Threat detection using behavior analytics, anomaly detection, and threat intelligence.
- Triage and investigation: validate alerts, enrich with context, and prioritize by impact.
- Response: containment guidance (or action), remediation support, and incident closure.
- Continuous improvement: tuning rules, reducing noise, and improving playbooks.
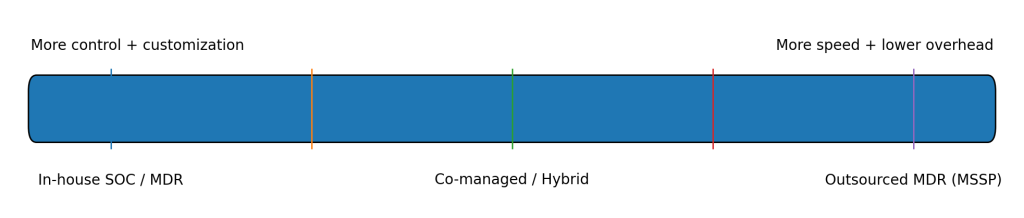
Your operating model options
Most organizations land in one of these three models:
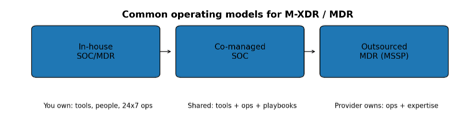
Option 1: Build it in-house (your own SOC/MDR)
If you go in-house, you’re signing up to own both the tech stack and the people side. That usually means:
- Purchasing and integrating essential tools such as SIEM, SOAR, EDR/XDR, ticketing, threat intelligence, and asset inventory is necessary.
- It is crucial to hire and retain analysts/engineers to ensure 24×7 coverage, while also having a plan in place for potential attrition.
- Develop playbooks, escalation paths, and incident processes that align with your business risk.
The upside is control: you can tailor detections, response actions, and priorities to your business—especially if your environment is unique or heavily regulated. The downside is cost and time-to-maturity.
Option 2: Outsource MDR (MSSP-run)
With outsourced MDR, a provider runs the day-to-day detection and response operations under a contract, measured by your SLOs and KPIs. Typically, they handle:
- Monitoring, detection, triage, and first-line investigation.
- Escalation and coordination during incidents (and sometimes direct containment actions).
- Threat intel-driven updates based on what they see across multiple customers.
The upside is speed and coverage without building a full SOC from scratch. The tradeoff is giving up some control—especially around alert handling, prioritization, and how “close to the keys” the provider gets.
How to decide: the factors that actually matter
Use this as a grounded checklist. If you’re honest about these, the answer usually becomes obvious.
| Factor | In-house is a better fit when… | Outsourced is a better fit when… |
| Budget | You can fund tools + integration + 24×7 staffing (OPEX and CAPEX). | You want predictable subscription costs and less upfront spend. |
| Staffing / skills | You can recruit/retain analysts and engineers and run shifts. | You’re lean, hiring is slow, or you need instant expertise. |
| Ownership & control | You need tight control of detections, response actions, and data. | You’re okay with shared control if outcomes and metrics are strong. |
| Speed to value | You can accept a longer ramp-up to build maturity. | You need coverage now (weeks, not quarters). |
| Risk tolerance | You prefer to own the risk and customize deeply. | You want to transfer operational burden to a proven provider. |
| Complexity / uniqueness | Your environment is highly custom, niche, or requires bespoke detections. | Your environment is fairly standard and maps well to provider playbooks. |
Outsourcing MDR: the real pros and cons
Pros:
- Lower overhead: less tooling sprawl and fewer hiring/training costs.
- Access to specialists who see attacks across multiple orgs (faster pattern recognition).
- Scales up/down as your environment changes.
- Better coverage for nights/weekends without burning out your team.
Cons:
- Less direct control over triage decisions and closure criteria.
- Communication friction (time zones, handoffs, language, context gaps).
- Provider compromise becomes your risk too—vendor security must be verified.
- You still need internal owners for incident response, IT ops, and business decisions.
Practical recommendation (what usually works)
For most organizations, the best answer is not “all in-house” or “fully outsourced.” It’s a hybrid that keeps decision-making internal and uses the provider for scale and depth. Examples:
- Co-managed SOC: provider monitors + triages; your team owns response and final decisions.
- Outsource first, then insource: start with MDR for coverage, build internal maturity over 12–24 months.
- In-house for crown jewels: keep critical systems under internal monitoring and outsource the rest.
If you outsource: minimum due diligence checklist
- Clear scope: what telemetry sources are included (endpoint, cloud, identity, email, network).
- Response model: advisory only vs hands-on containment (and who approves actions).
- Metrics that matter: MTTD/MTTR targets, alert quality (false positive rate), escalation SLAs.
- Data handling: where logs are stored, retention, encryption, access controls, and segregation.
- Provider security posture: SOC 2 / ISO 27001, pen tests, incident history, subcontractors.
- Runbooks + playbooks: prove they align to your incident management policy.
- Exit plan: how you get your data, detections, and workflows back if you terminate.
Bottom line
There’s no one-size-fits-all answer. If you have budget, talent, and a need for deep control, in-house can be the right call. If you need fast, reliable coverage with less operational drag, outsourced MDR wins. If you want the best balance, go hybrid: keep ownership of risk decisions internally and buy scale from a trusted provider.